Security headers are HTTP response headers that instruct the browser how to behave when handling your site's content. Missing or misconfigured headers are a quiet but persistent risk — they expose your site to clickjacking, MIME sniffing, cross-site scripting, and other client-side attacks.
Why SEO teams should care
Google measures trust signals and site quality as part of ranking. Security headers are a direct indicator of technical hygiene. More importantly, a compromised or injected page can quietly harm your organic rankings, user trust, and conversion — often before you detect it manually.
The six headers that matter most
-
Strict-Transport-Security (HSTS) — Forces HTTPS connections and prevents protocol downgrade attacks.
Adding
includeSubDomainsextends protection across all subdomains. -
X-Content-Type-Options — Set to
nosniffto prevent browsers from guessing MIME types, blocking drive-by-download attacks. -
X-Frame-Options — Controls whether your pages can be embedded in iframes. Use
SAMEORIGINorDENYto block clickjacking. - Content-Security-Policy (CSP) — The most powerful header. Restricts which scripts, styles, and resources the browser can load. Effective CSP is your primary XSS defense.
-
Referrer-Policy — Controls how much referrer information is passed to third parties.
strict-origin-when-cross-originis the recommended modern default. - Permissions-Policy — Restricts access to browser APIs like camera, microphone, and geolocation from your pages and embedded iframes.
How scoring works
Each header contributes to a 0–100 security score. The grade (A through F) reflects the overall coverage:
- HSTS: 20 points (+5 bonus for
includeSubDomains) - X-Content-Type-Options: 15 points
- X-Frame-Options: 15 points
- Content-Security-Policy: 25 points
- Referrer-Policy: 15 points
- Permissions-Policy: 10 points
A score of 90+ earns an A. Below 25 is an F. The goal is not a perfect score — it's knowing your current baseline and tracking regressions before they affect users.
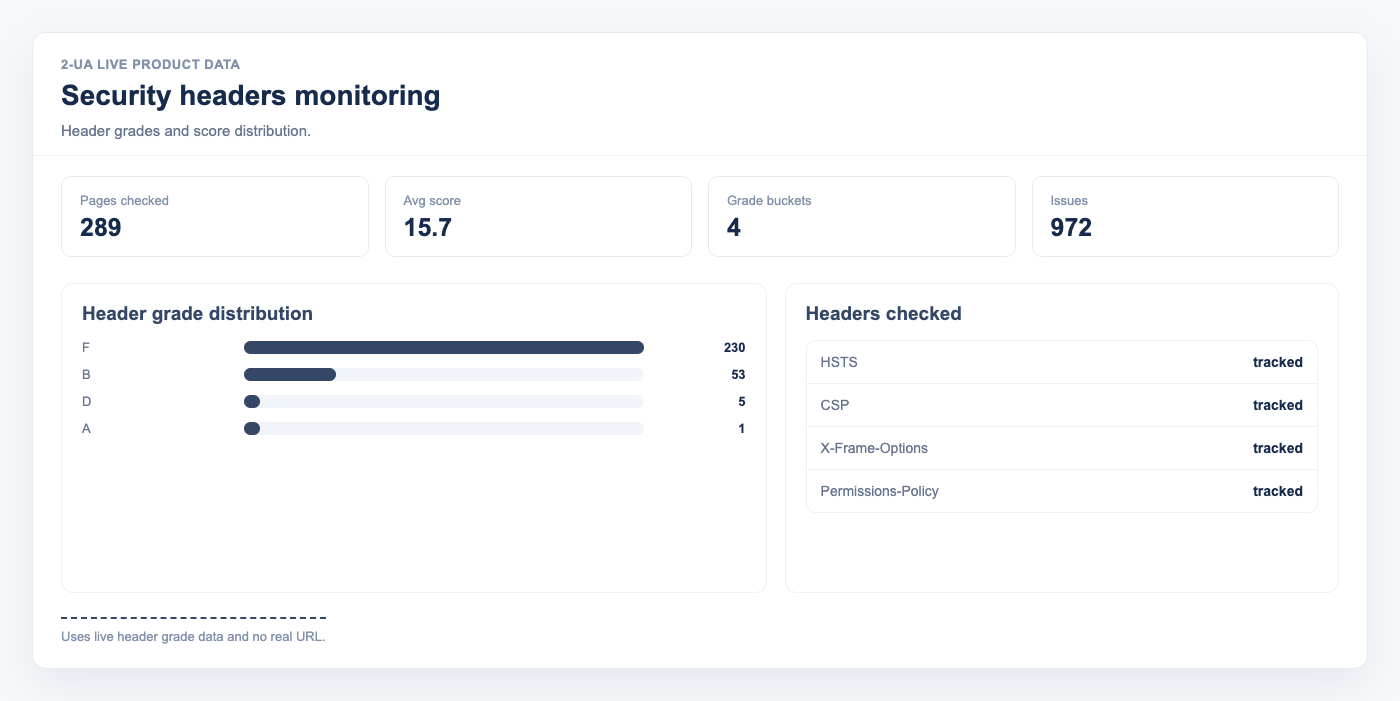
How 2-UA collects security headers
Security headers are collected automatically during every desktop content check of your tracked URLs. No extra configuration is needed. Open any tracked URL and choose Security headers from the Quick menu to see the current grade, score, and per-header breakdown.
The site-wide summary view shows all your tracked URLs ranked by security score, making it easy to prioritize which pages need attention first.
Practical monitoring workflow
- Run a content check for your critical tracked URLs.
- Open the Security headers view and check the grade column.
- For any header marked Missing, apply the recommendation shown in the detail view.
- After deploying the fix, the next content check will automatically update the score.
- Use the site-wide summary to confirm all important pages stay at grade B or higher.
Security regressions — like a CSP header being removed after a deployment — are easy to miss manually. Recurring automated checks catch these the moment they happen.
Stop losing SEO performance to silent changes
If this workflow matches your current SEO bottleneck, do not postpone implementation. Teams usually lose the most traffic between detection and action, not between action and resolution. Start monitoring today and create your first baseline in under an hour.
Execution blueprint for security headers monitoring
Long-form SEO implementation fails when teams try to “fix everything” at once. The sustainable approach is to define a narrow execution lane, prove measurable movement, and scale based on validated impact. For site reliability workflows, this usually means setting explicit ownership, reporting cadence, and escalation thresholds.
A useful way to operationalize this is to split work into three layers: detection, validation, and rollout. Detection finds anomalies quickly. Validation confirms whether the anomaly is material or incidental. Rollout converts validated findings into engineering and content tasks with deadlines. If one layer is missing, the process becomes either noisy or slow.
90-day rollout plan
Days 1-14: baseline and instrumentation
- Define the monitored scope: templates, critical URLs, and ownership groups.
- Set expected behavior for status codes, redirects, and indexation-relevant rules.
- Enable alerts in your team channel and set an initial noise-control policy.
- Run the first full crawl and preserve it as a technical baseline snapshot.
- Document the current known issues so future alerts can be triaged faster.
Days 15-45: controlled improvement
- Move from URL-level fixes to issue-family fixes (template/system level).
- Review trends weekly for response time, quality checks, and crawl findings.
- Introduce tag-based segmentation if your team supports multiple page clusters.
- Track fix validation in re-crawls and keep a short evidence log for each change.
- Escalate only high-impact regressions to engineering to avoid context switching overload.
Days 46-90: scale and commercialization
- Standardize recurring reports for stakeholders and client-facing communication.
- Harden your alert policy with quieter thresholds and clear severity levels.
- Expand monitoring from critical templates to full coverage where justified.
- Turn recurring findings into preventive engineering tasks, not one-off tickets.
- Connect technical trend movement to revenue-adjacent metrics for executive buy-in.
Measurement model: what to track weekly
You should define a compact KPI stack that reflects both technical quality and operational speed. Over-measuring creates reporting overhead and weakens decision quality. A practical KPI model for this topic includes:
- Detection speed: time from change occurrence to first alert.
- Triage speed: time from alert to issue classification and owner assignment.
- Resolution speed: time from assignment to verified fix.
- Regression rate: how often a fixed issue class returns within 30 days.
- Coverage quality: share of critical pages included in active monitoring.
- Business relevance: proportion of high-impact issues in total issue volume.
For mature teams, the strongest KPI is not total issue count but high-impact issue recurrence. When recurrence falls, process quality is improving.
Stakeholder alignment framework
Technical SEO execution usually fails at the handoff boundary. SEO specialists detect issues, but engineering sees isolated tasks without business context. Fix this by sending implementation-ready summaries:
- What changed (objective signal, not interpretation).
- Where it changed (template, segment, or specific URL class).
- Why it matters (indexation, visibility, trust, conversion risk).
- What to do next (single recommended action with acceptance criteria).
- How to verify (which re-check confirms the fix).
If your company runs weekly planning, summarize this in one page before sprint grooming. If you run continuous delivery, post a compact incident card into Slack or ticketing with direct links.
Common failure patterns and how to avoid them
- Too much scope: teams monitor everything and fix nothing. Start with critical assets.
- No baseline: every alert feels urgent without a reference snapshot.
- Tool-only mindset: dashboards do not create outcomes without process ownership.
- One-channel reporting: executives and implementers need different output layers.
- No post-fix validation: “done” without re-check creates hidden regressions.
Operational checklist you can reuse
- Confirm scope and ownership for monitored entities.
- Establish expected behavior and escalation policy.
- Launch baseline checks and preserve initial state.
- Run weekly issue-family review with implementation owners.
- Validate completed fixes with scheduled re-checks.
- Report only high-signal movements to leadership.
- Iterate thresholds every 2-4 weeks based on false-positive rate.
Commercial impact: turning technical work into revenue protection
Teams buy monitoring platforms when they can prove one thing: technical signals reduce preventable loss and shorten recovery time. In practice, you can demonstrate this by documenting incidents prevented, recovery cycles reduced, and implementation throughput improved.
This is where aggressive execution beats passive auditing: instead of producing occasional reports, you build an operating system for technical SEO quality. Once that system is in place, scaling to more URLs, more sites, and more stakeholders becomes predictable.
Advanced FAQ for security headers monitoring
How much historical data is enough for reliable decisions?
For most SEO teams, 4 to 8 weeks of consistent monitoring is enough to separate random fluctuation from structural movement. If your release velocity is high, use shorter review cycles but keep a rolling 8-week reference window. The key is consistency: gaps in monitoring reduce interpretability more than imperfect metrics.
Should we optimize for issue count reduction or impact reduction?
Always optimize for impact reduction. Lower issue count can be misleading if high-severity classes remain unresolved. In mature workflows, teams track high-impact recurrence, time-to-resolution, and incident spread by template class.
What is the best cadence for reporting this topic to leadership?
Weekly operational review plus a monthly executive summary works best. Weekly reports should focus on changes, actions, and blockers. Monthly reports should focus on trend direction, prevented incidents, and business-risk reduction. This two-layer model avoids both over-reporting and under-reporting.
How do we keep collaboration smooth with engineering teams?
Convert every finding into an implementation-ready task: define affected scope, expected behavior, acceptance criteria, and verification method. Engineering teams respond faster when tasks are deterministic. Avoid sending raw issue exports without business context.
When should we escalate from soft monitoring to stricter controls?
Escalate when any of the following is true: critical template regressions appear repeatedly, recovery time is increasing, or ownership is unclear across incidents. At that point, tighten alert policy, enforce scope ownership, and add stricter verification gates after releases.
How do we evaluate ROI for this workflow?
ROI appears in three layers: lower incident duration, fewer recurring regressions, and improved implementation confidence across teams. For stakeholder communication, quantify prevented loss events and reduced recovery effort rather than raw technical counts. This framing translates technical monitoring into business language that supports budget decisions.